The edge relies on the infrastructure to read state data: balances, transaction status, historical holdings, DeFi yields, AMM exchange rates, …
Simply reading part of the state reveals users' holdings and intentions, and undermines privacy protections like shielding.
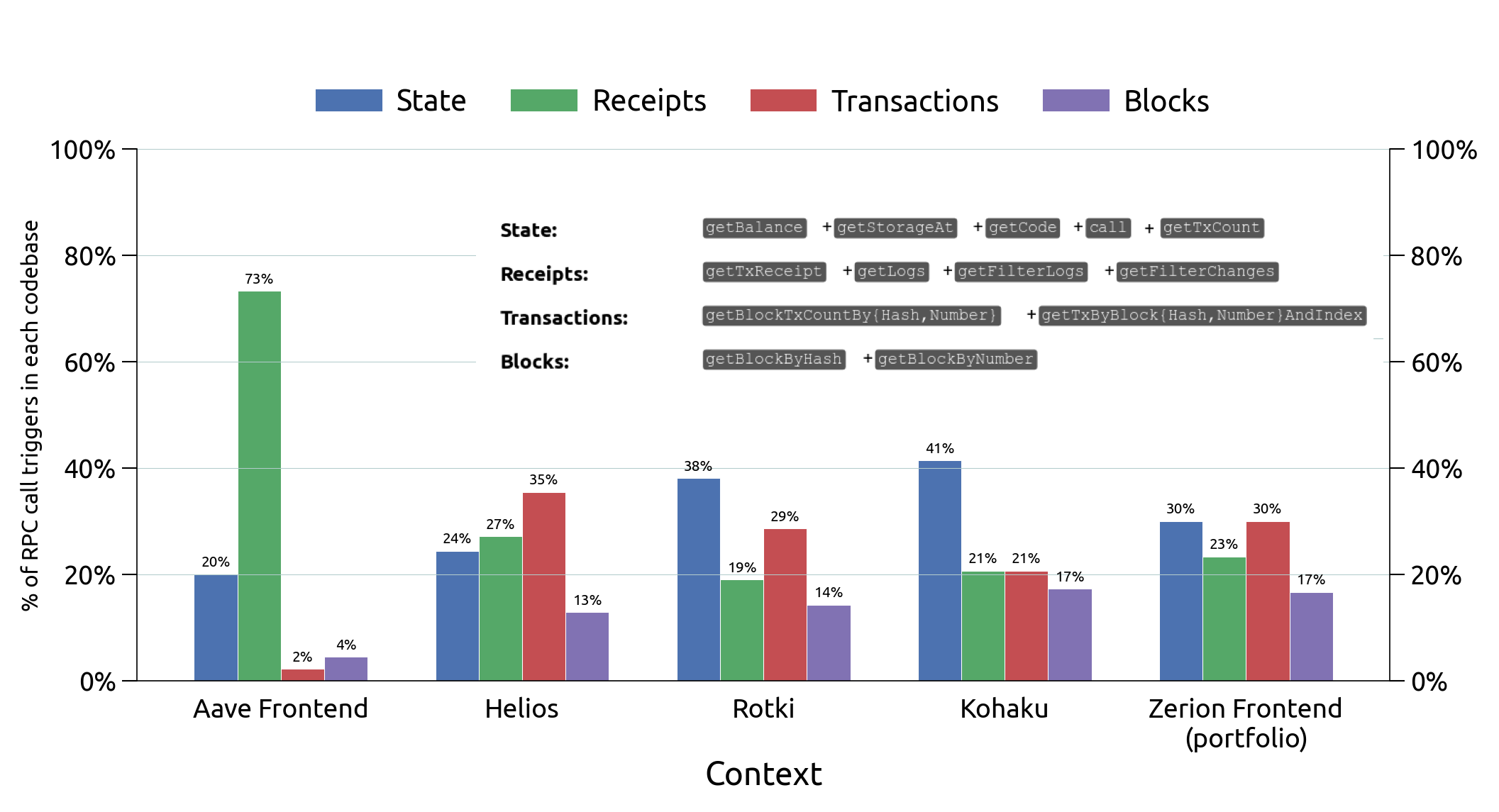
Answer: a bit of everything
Our current focus is single-server PIR
The server answers queries while being completely oblivious to what is being accessed or what the query is about
Various cryptographic tools to achieve this hiding; example from FHE-based schemes:
The most consequential factors: database size and (for some schemes) update frequency
Meanwhile, looking at Ethereum data:
The most consequential factors: database size and (for some schemes) update frequency
Example: use a
server- and client-stateless scheme for
"Express" because:
(a) it's consumed frequently in frontends (can't have client-side
storage assumption)
(b) latency sensitive
(c) small in size so the performance should be ok despite query cost
being linear in db size
Each slice (shard) is paired with the optimal scheme (engine) … but all schemes must be queried in parallel with decoy queries in addition to the real query, to preserve privacy
Note: more bandwidth is consumed but since the queries are independent, it doesn't affect the latency of the real query